[ STATUS: LIVE RECONNAISSANCE LOG ]
The Scraping Trap
A chronological breakdown of how a public email address was harvested, enriched, and targeted within 7 days of site launch.
Initial Deployment
During functionality testing, contact@get-it.uk was published in the site footer.
Link Removal & Initial Spam
The email link was removed as part of hardening. However, the data was already sold.
Brand Impersonation Payload
The attack evolved. By cross-referencing our domain's MX records, threat actors identified Zoho as our service provider.
EXHIBIT: PHISH-ZOHO-01
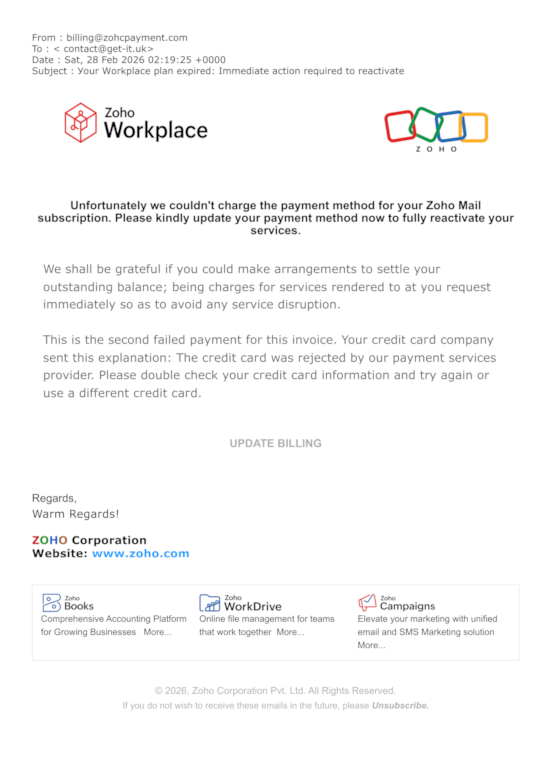
Forensic Analysis: Red Flags
- Homograph Domain Attack: The sender address used
zohcpayment.com. - Cyrillic Character Substitution: Subject line utilized Cyrillic characters to evade filters.
The Project Fortress Solution
This incident is exactly why GET-IT does not use public-facing email links.
Secure My Domain →